For years, the standard operating procedure for developers integrating large language models has been a frantic dance with regular expressions. To prevent sensitive user data from leaking into a prompt, engineers have spent countless hours crafting complex regex patterns to catch every possible variation of an email address or phone number. It is a fragile system where a single misplaced character in a user's input can bypass the filter, sending personally identifiable information (PII) straight to a cloud server. This week, the conversation in the developer community shifted as a new tool emerged that promises to replace these rigid rules with local, context-aware intelligence.
The Architecture and Performance of Privacy Filter
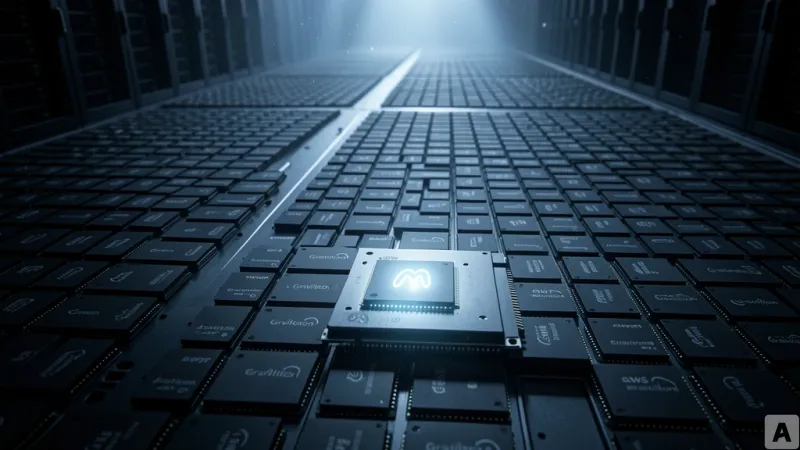
OpenAI has released Privacy Filter, an open-weight model specifically engineered for the detection and masking of PII. The model is designed for extreme efficiency, featuring a total of 1.5B parameters, though it only utilizes 50M active parameters during actual computation. This lean profile allows it to run locally on modest hardware while maintaining a massive context window of up to 128,000 tokens. Distributed under the Apache 2.0 license, the model is available for commercial use and modification via Hugging Face and GitHub.
The model targets eight distinct categories of sensitive information: `private_person`, `private_address`, `private_email`, `private_phone`, `private_url`, `private_date`, `account_number` (which covers credit cards and bank accounts), and `secret` (which includes passwords and API keys). The performance metrics are substantial. On the PII-Masking-300k dataset, the model recorded an F1 score of 96%. In a version where annotation issues were corrected, the performance climbed further to an F1 score of 97.43%, with a precision of 96.79% and a recall of 98.08%. One of the most striking aspects of the model is its capacity for domain adaptation; when fine-tuned with a small amount of specialized data, its F1 score jumped from 54% to 96%, demonstrating a high degree of flexibility across different industries.
Technically, Privacy Filter operates as a bidirectional token classification model combined with span decoding. It began as an autoregressive pre-training checkpoint that was subsequently adapted into a token classifier using a fixed privacy label system. Rather than generating text token by token, the model labels the entire input sequence simultaneously. It then employs a constrained Viterbi procedure to restore consistent spans, ensuring that the boundaries of the detected PII are precise. Because the model processes all tokens in a single forward pass, inference speed is exceptionally high. The final output is decoded using BIOES span tags, which explicitly mark the beginning, inside, outside, end, and single-token status of each entity, resulting in clean and accurate masking boundaries.
From Rigid Rules to Contextual Engineering
The release of Privacy Filter represents a fundamental shift in how the industry handles data sanitization. For a long time, the reliance on rule-based detection meant that tools were blind to context. A regex pattern can identify a string that looks like an email, but it cannot distinguish between a public corporate contact address that should remain visible and a private user email that must be hidden. By moving toward a model that understands language and context, developers can now differentiate between public information and sensitive data based on how the text is actually used.
This shift fundamentally alters the data pipeline. Previously, many organizations relied on third-party anonymization APIs, which created a paradoxical security risk: to protect the data, they had to send it to another external server. Privacy Filter eliminates this tension by enabling local execution. The raw, unmasked data never leaves the local device or the secure internal environment, ensuring that the filtering process itself does not become a point of vulnerability. Furthermore, because the model was trained on a blend of public and synthetic data, it is better equipped to handle the messy, unpredictable patterns of real-world privacy leaks than any static list of rules.
However, this tool is not a total replacement for legal compliance frameworks. It is a technical filter, not a certified anonymization tool or a legal guarantee of compliance. In high-stakes environments such as healthcare or legal services, where a single missed token can have severe regulatory consequences, human oversight and further domain-specific fine-tuning remain mandatory. The model provides the engineering foundation for privacy, but it does not replace the need for a comprehensive privacy policy.
Privacy is no longer just a matter of policy and checkboxes; it has become a precision engineering challenge that can be solved locally.