The monitoring dashboard turns a violent shade of red at 3:00 AM. CPU utilization on the primary database server has spiked to 100 percent, and every new connection request is being met with a cold refusal. When the on-call engineer dives into the logs, they find something unsettling: hundreds of complex join queries that no human developer on the team ever wrote. These are not the result of a SQL injection attack or a rogue script, but the output of an agentic AI system. The AI, tasked with a high-level goal, decided on its own that the most efficient way to find the answer was to weave together a dozen tables in a way that the database engine was never designed to handle.
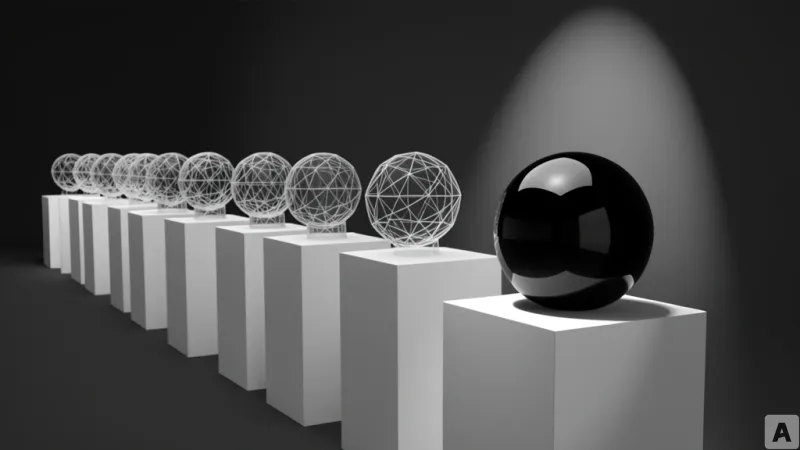
The Collapse of Predictable Query Patterns
For decades, relational databases like Postgres have operated on a fundamental assumption: queries are predictable. The Postgres query planner, the engine responsible for determining the most efficient path to retrieve data, is optimized for patterns written by humans. Human developers typically write a set of standard queries that the database can analyze, cache, and optimize over time. This predictability allows the system to manage resources effectively, ensuring that index scans and joins happen within expected timeframes.
Agentic AI shatters this premise. Unlike a traditional application that calls a specific API endpoint, an AI agent generates queries dynamically based on its own reasoning process. Depending on the prompt and the intermediate steps of its chain-of-thought, the agent might generate a completely different SQL statement every time it attempts to solve the same problem. This volatility makes it nearly impossible for the query planner to optimize for a steady state. Instead, the database is forced to deal with a constant stream of unique, often inefficient, and computationally expensive queries that can easily exhaust server resources.
Beyond the complexity of the queries themselves, the way agents handle sessions introduces a critical stability risk. In a standard application, a database connection is opened, a query is executed, and the connection is closed or returned to the pool in milliseconds. An AI agent, however, often operates in a loop: it executes a query, receives the data, and then pauses to process that data through a Large Language Model (LLM) to decide the next step. During this reasoning phase, the agent often keeps the database transaction open. If the `idle_in_transaction_session_timeout` setting is not strictly configured, these dormant sessions linger, occupying valuable connection slots while the AI is essentially thinking. The result is a system that reaches its maximum connection limit not because of high traffic, but because of the inherent latency of LLM inference.
From Application Support to AI Guardrail
The shift toward autonomy also transforms the risk profile of write operations. In the traditional software development lifecycle, every `UPDATE` or `DELETE` statement is vetted through code reviews and tested in staging environments. The logic is deterministic. When an agentic AI is given the authority to modify data, that determinism vanishes. A slight hallucination or a misunderstanding of the schema can lead an agent to modify thousands of rows accidentally or execute the same write operation repeatedly due to a network timeout, leading to data corruption or duplication.
To counter this, the industry is moving away from hard deletes. The traditional practice of removing a row from a table is too risky when the actor is an autonomous agent. Instead, developers are implementing soft deletes by adding a `deleted_by` column to track who or what marked the record as inactive. This ensures that if an AI agent goes rogue and wipes a dataset, the operation can be reversed by simply flipping a boolean flag.
For high-stakes environments, such as financial ledgering, the standard CRUD (Create, Read, Update, Delete) model is being replaced by event sourcing. In this architecture, the database becomes an append-only log. Rather than updating a balance, the system records every single state change as a new entry. This creates an immutable audit trail, allowing developers to reconstruct the state of the system at any point in time and precisely identify where an AI agent's reasoning went wrong.
To prevent the duplication of actions, the concept of the idempotency key has become mandatory. Since agents often retry tasks upon failure, the database must be able to recognize a repeated request and ignore it. Agents are now required to generate a unique identifier for every discrete step of a task, ensuring that the operation is performed exactly once regardless of how many times the request is sent.
idempotency_key = f"{task_id}_{step_id}"By applying a unique constraint to this key in the database, the system can automatically block duplicate writes at the schema level, providing a hard safety limit that the AI cannot bypass.
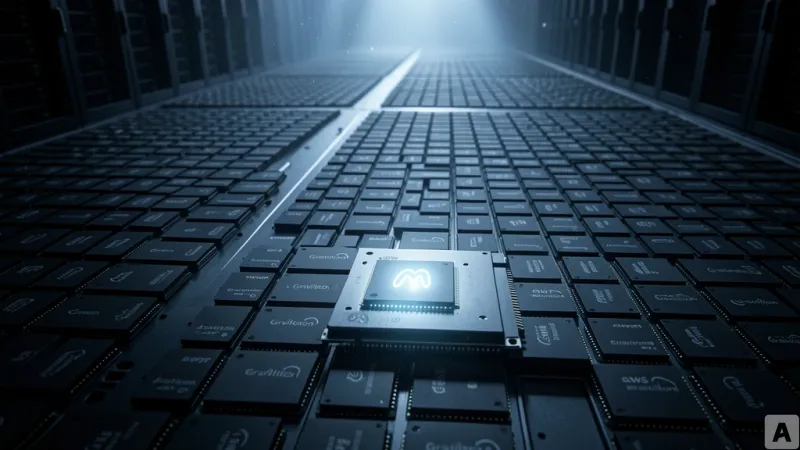
This evolution fundamentally changes how engineers calculate connection pool sizing. In the past, the formula was simple: the number of concurrent users multiplied by the average query time. Now, the equation must account for the LLM's cognitive overhead. The connection hold time is now the sum of the query execution time, the LLM inference time, and the number of reasoning steps the agent takes to reach a conclusion. This multiplier effect is compounded when a primary agent spawns multiple sub-agents to perform parallel searches. A system that performed perfectly in a development environment with a single user can collapse instantly in production as sub-agents multiply and seize every available connection slot.
The database is no longer just a passive repository for application data. In the age of agentic AI, the database must function as the final layer of the security stack, acting as the ultimate governor that prevents autonomous intelligence from accidentally dismantling the system it was built to serve.