Chief Information Security Officers at Fortune 500 companies currently face a paradoxical struggle. They are under immense pressure to integrate Large Language Models into their workflows to drive productivity, yet they are terrified of the data leakage that comes with it. The risk is concrete: a customer's home address, a private phone number, or a proprietary internal ID slipping into a prompt and ending up on a third-party server. For years, the industry has relied on a binary choice between fragile regular expressions that miss context and massive LLMs that are too slow and expensive to act as a first-line defense. This week, the arrival of the OpenAI Privacy Filter suggests a third path, moving the security perimeter from the cloud gateway directly to the user's device.
The Architecture of Localized Privacy
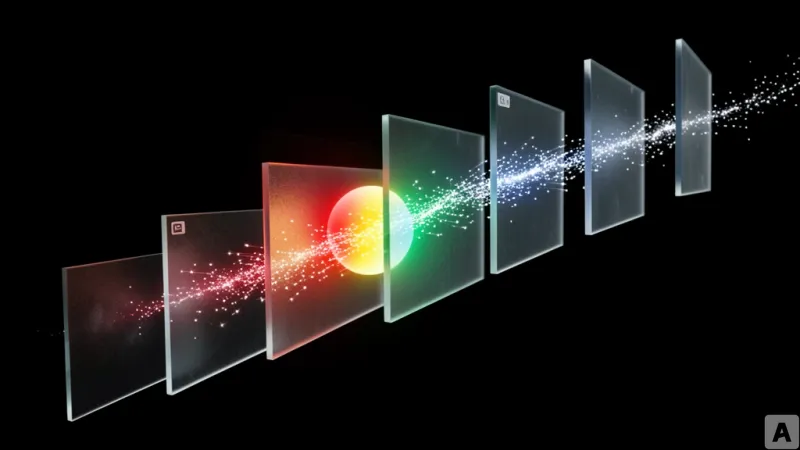
OpenAI Privacy Filter is not a generative model in the traditional sense but a specialized bidirectional token-classification system designed to detect and mask personally identifiable information (PII). The model is built with a total of 1.5 billion parameters, but its efficiency stems from a sparse architecture where only 50 million parameters are active during actual computation. This lean profile allows the model to run on standard laptops or even within a web browser without requiring a dedicated high-end GPU. To ensure wide adoption and transparency, the model is released under the Apache 2.0 license, permitting everything from academic research to full-scale commercial deployment.
The training pipeline follows a sophisticated multi-stage process. It begins with autoregressive pre-training using a structure similar to the gpt-oss model. Once the base linguistic understanding is established, the model is converted into a token classifier utilizing bidirectional banded attention. This specific mechanism uses a band size of 128, allowing the model to analyze a window of 257 tokens simultaneously to determine the context of any given word. To finalize the detection, the system employs the Viterbi procedure, an optimization algorithm that finds the most probable sequence of labels. This results in BIOES labeling—Begin, Inside, Outside, End, and Single—which allows the model to precisely delineate where a piece of PII starts and ends across eight distinct output categories.
For developers working in Python, the model is accessible via the Transformers library. A basic implementation for token classification looks like this:
from transformers import pipelineclassifier = pipeline(
task="token-classification",
model="openai/privacy-filter",
)
classifier("My name is Alice Smith")
In production environments where granular control over the tensor flow is required, developers can call the AutoModelForTokenClassification class directly to handle the logits and label mapping:
import torch
from transformers import AutoModelForTokenClassification, AutoTokenizertokenizer = AutoTokenizer.from_pretrained("openai/privacy-filter")
model = AutoModelForTokenClassification.from_pretrained("openai/privacy-filter", device_map="auto")
inputs = tokenizer("My name is Alice Smith", return_tensors="pt").to(model.device)
with torch.no_grad():
outputs = model(**inputs)
predicted_token_class_ids = outputs.logits.argmax(dim=-1)
predicted_token_classes = [model.config.id2label[token_id.item()] for token_id in predicted_token_class_ids[0]]
print(predicted_token_classes)
Moving the Perimeter to the Client Side
The critical shift here is the movement away from pattern matching toward contextual understanding. Traditional PII filtering relies heavily on regular expressions (regex), which are essentially static templates. Regex can find a string that looks like an email address, but it cannot distinguish between a fake example email in a technical manual and a real customer email in a support ticket. Conversely, using a frontier model like GPT-4 for this task is computationally ruinous and introduces the very privacy risk the filter is meant to prevent. The OpenAI Privacy Filter occupies the goldilocks zone: it is small enough to be local but smart enough to understand context.
One of the most significant technical advantages is the context window. The model can process up to 128,000 tokens in a single pass. This is a massive leap for enterprise utility, as it allows the system to ingest entire legal contracts or massive system log files without the need to chunk the data, which often breaks the context of PII entities. Furthermore, the model allows for a tunable balance between precision and recall. In a high-security environment, a developer can tune the model for higher recall to ensure no PII ever escapes, even at the cost of some false positives. In a high-throughput environment, they can prioritize precision to reduce friction.
The most disruptive element, however, is the integration with Transformers.js. By leveraging WebGPU, the filtering process can happen entirely within the user's browser. This means sensitive data is masked before it ever leaves the client's RAM, effectively neutralizing the risk of transit-layer leaks.
import { pipeline } from "@huggingface/transformers";const classifier = await pipeline(
"token-classification", "openai/privacy-filter",
{ device: "webgpu", dtype: "q4" },
);
const input = "My name is Harry Potter and my email is [email protected].";
const output = await classifier(input, { aggregation_strategy: "simple" });
console.dir(output, { depth: null });
By shifting the computation to the edge, the model removes the cloud as a single point of failure for privacy. The data is scrubbed at the source, and the enterprise only receives the sanitized version of the input.
This transition toward lightweight, specialized local models marks the end of the era where privacy was a cloud-side configuration and begins the era of client-side enforcement.