The morning started with a routine git push for thousands of developers worldwide. For many, the workflow was seamless until they checked their Vercel dashboards. Instead of the usual green deployment checkmarks, red warning lights began to flicker across the screen. Sites that had been stable for months suddenly returned 504 Gateway Timeout errors or failed to deploy entirely. The community initially assumed it was a standard regional outage or a botched platform update, but the reality was far more calculated. A single actor had found a way to turn the very efficiency of the modern cloud against itself.
The Anatomy of an AI-Driven Infrastructure Collapse
The disruption was not the work of a state-sponsored hacking group or a massive botnet of infected IoT devices. Instead, the source was a developer specializing in creating cheats and hacks for Roblox. This individual leveraged a sophisticated AI automation tool to launch a targeted assault on Vercel's global infrastructure. Unlike traditional attacks that rely on sheer volume, this operation utilized AI to generate a stream of highly complex, mutating requests that targeted Vercel's edge nodes.
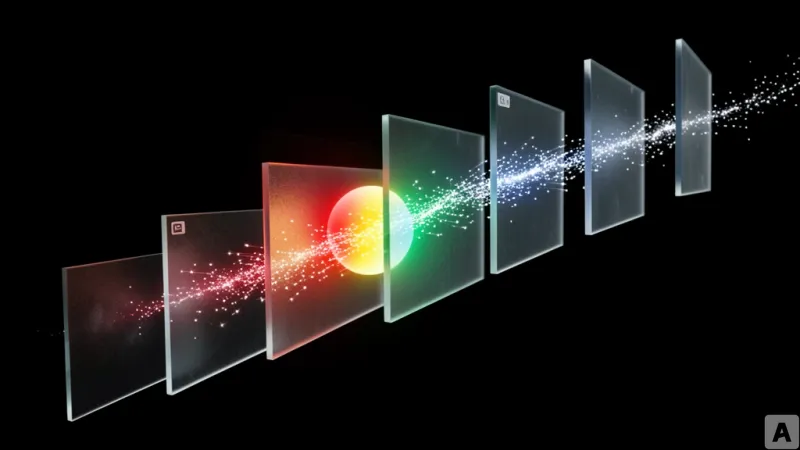
These requests were not static. The AI tool was programmed to modify request headers in real-time, effectively rotating the identity and characteristics of each packet to bypass standard security filters. By constantly shifting the pattern of the traffic, the attacker ensured that the requests looked like legitimate, diverse user behavior rather than a coordinated attack. This caused a massive surge in resource consumption across Vercel's Edge Network, the distributed layer of servers designed to deliver content to users with minimal latency. As the edge nodes struggled to process these computationally expensive requests, the system's available resources were exhausted, leading to a cascading failure that slowed response times to a crawl and eventually knocked entire services offline.
From Brute Force to Algorithmic Precision
To understand why this attack succeeded where traditional defenses usually prevail, one must look at the evolution of the Denial of Service attack. A standard DDoS attack is a game of numbers; it is the digital equivalent of ten thousand people trying to push through a single narrow door at the same time. The goal is to overwhelm the entry point through sheer mass. Vercel and other cloud giants have spent years perfecting rate-limiting and traffic-shaping tools to stop this specific behavior. If a single IP address sends a million requests per second, the system simply closes the door.
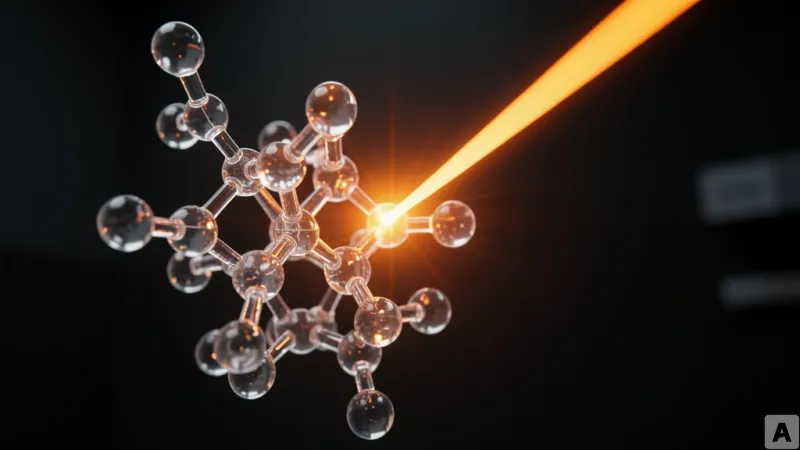
This attack, however, operated on the principle of precision rather than volume. The AI did not try to break the door down; it analyzed the lock. By observing how the Edge Network responded to different inputs, the AI learned the specific rules the filtering system used to distinguish between a human and a bot. It then automatically synthesized request patterns that mirrored the exact characteristics of a valid user. This turned the Edge Network's greatest strength—its ability to handle diverse, global traffic—into a vulnerability. The system accepted the malicious traffic because it looked exactly like the traffic it was designed to optimize.
The most critical point of failure was the exploitation of serverless functions. In a serverless architecture, code executes in response to an event, similar to a vending machine that only activates when a button is pressed. The AI tool discovered the digital equivalent of the most complex menu item in that vending machine—a specific combination of inputs that required maximum CPU and memory to process. By flooding the system with these high-cost requests, the attacker forced the serverless environment to spin up maximum resources for every single call. This created a resource exhaustion loop where the infrastructure spent more time trying to manage the overhead of the requests than actually serving the content.
This shift marks a dangerous transition in cybersecurity. The attacker no longer needs a botnet of a million compromised computers to bring down a tier-one cloud provider. A single operator with a powerful AI model can now conduct an algorithmic complexity attack that mimics legitimate traffic so perfectly that traditional volume-based defenses become obsolete. The attack proved that when AI is used to map the internal logic of a cloud provider's routing and execution layers, it can find the exact frequency needed to shatter the system.
Cloud infrastructure defense must now move beyond rate-limiting and toward behavioral AI that can detect the subtle, mathematical signatures of synthetic traffic.