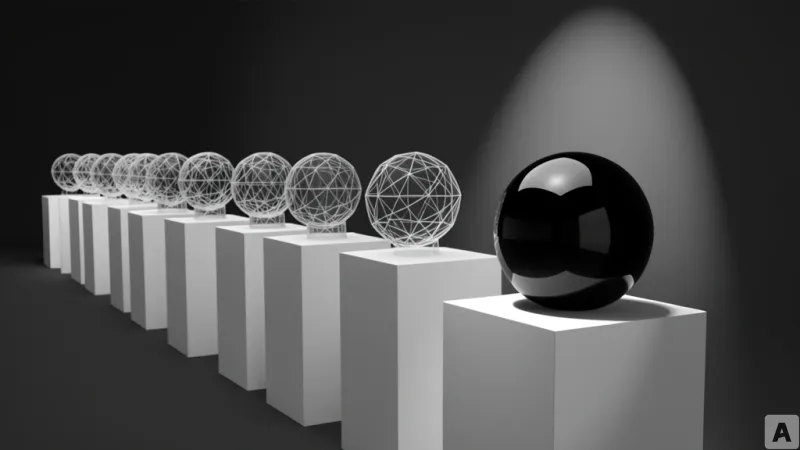
Every morning, the cycle repeats across the modern engineering org. A developer installs GitHub Copilot to accelerate a sprint, a data analyst feeds a proprietary dataset into a new LLM to generate a quarterly report, and a product manager quietly integrates a third-party API into a feature branch to hit a deadline. By the time the security team discovers these tools, the AI is already live in production, processing real customer data, accessing internal systems, and making autonomous decisions. This friction between the velocity of AI adoption and the inertia of corporate governance is where the most critical vulnerabilities emerge.
The Blueprint for AI Visibility and Risk Quantification
Mend addresses this systemic gap with a new operational guide titled AI Security Governance: A Practical Framework for Security and Development Teams. Rather than assuming an organization already possesses a mature security program, the framework is built for the people currently in the trenches—AppSec leads, engineering managers, and data scientists who know they need a strategy but lack a starting point. The foundation of the framework rests on the premise that you cannot control what you cannot see. To combat Shadow AI, Mend defines a broad scope of AI assets that must be inventoried, including AI development tools like Copilot and Codeium, third-party APIs from OpenAI and Google Gemini, open-source models, and embedded AI features within SaaS platforms like Notion AI. Crucially, the framework argues that the discovery of these tools should not be a punitive process, but rather a safe disclosure mechanism that encourages transparency over evasion.
Once assets are identified, the framework moves away from a one-size-fits-all security posture. Instead, it implements a granular risk rating system where each AI asset is scored from 1 to 3 across five specific dimensions: data sensitivity, decision-making authority, system access privileges, external exposure, and supply chain origin. The resulting total score determines the required level of governance. A key insight here is that risk is dynamic; a model's risk profile can spike even if the underlying code remains unchanged. For instance, granting an AI agent write access to a production database or exposing a previously internal tool to external users can instantly elevate a tool from a low-risk Level 1 to a high-risk Level 3.
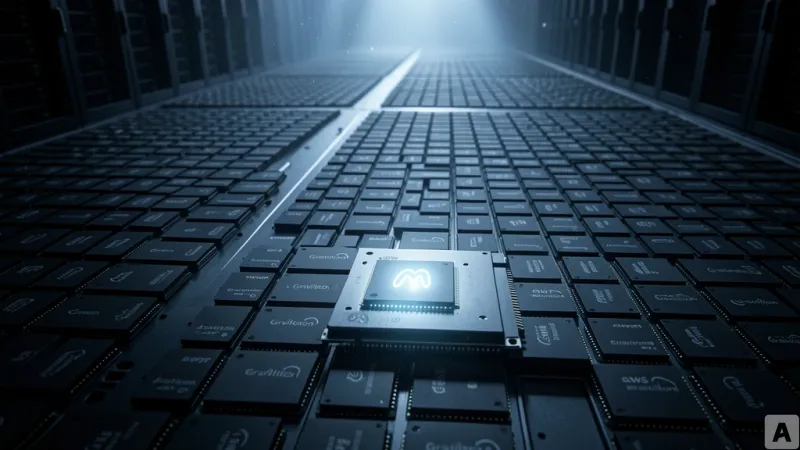
To manage the inherent risks of third-party dependencies, Mend introduces the AI-BOM, or AI Bill of Materials. This extends the traditional SBOM concept to include model artifacts, training datasets, fine-tuning inputs, and inference infrastructure. A comprehensive AI-BOM documents the model name, version, provenance, training data references, and all software dependencies required for execution, alongside known vulnerabilities and their remediation status. This level of transparency is not merely a best practice but a necessity for compliance with emerging regulations such as the EU AI Act and the NIST AI RMF, which explicitly demand supply chain transparency.
Shifting the Focus from Model Flaws to Access Control
While much of the industry focuses on the inherent flaws of LLMs, Mend's framework posits that the majority of AI security failures stem from poor access control rather than model instability. The solution is a rigorous application of the principle of least privilege. This means API keys must be scoped to specific resources, AI agents must never share credentials with human users, and read-only access should be the default unless write permissions are strictly necessary. The framework treats AI output with the same suspicion as user input. Because AI can reconstruct or infer sensitive information, the framework mandates output filtering for regulated data patterns, such as social security numbers, credit card details, and API keys. Furthermore, any code generated by AI is treated as untrusted input and must undergo the same security scanning pipeline as human-written code, specifically utilizing SAST, SCA, and secret scanning.
This shift in perspective extends to monitoring. Traditional SIEM rules, network-based anomaly detection, and endpoint monitoring are largely blind to AI-specific failure modes. Mend defines three distinct monitoring layers to close this gap. At the model layer, the focus is on detecting prompt injection attempts, system prompt extraction, and significant shifts in output confidence scores or patterns. At the application integration layer, the system monitors whether AI outputs are being routed to sensitive sinks—such as database writes or external API calls—and flags unusual spikes in API volume. Finally, at the infrastructure layer, the framework monitors for unauthorized access to model artifacts or training data stores and detects unexpected egress to unapproved external AI APIs.
To track progress, the framework provides a four-stage AI Security Maturity Model: Initial (Ad-hoc/Awareness), Developing (Defined/Reactive), Controlled (Managed/Proactive), and Leading (Optimized/Adaptive). This model maps directly to global standards including NIST AI RMF, OWASP AIMA, ISO/IEC 42001, and the EU AI Act. Most organizations currently reside in the Initial or Developing stages, a reality Mend views not as a failure, but as a natural consequence of AI adoption outstripping governance. The transition from Initial to Developing is centered on visibility: deploying the AI-BOM, assigning clear ownership, and establishing the non-punitive discovery process for Shadow AI.
Execution of these policies is integrated directly into the technical pipeline. This involves implementing SAST and SCA scanning within CI/CD workflows, enforcing network controls to block egress to unauthorized AI endpoints, and applying strict IAM policies to AI service accounts. By translating high-level principles into actionable code and policy, the framework moves AI security out of the realm of theoretical risk and into the realm of engineering reality.
This framework transforms AI security from a gatekeeping function into a collaborative engineering discipline where the AI-BOM and risk ratings serve as the common language between developers and security teams.