A security analyst opens a file named report.pdf. On the surface, it appears to be a standard document, the kind of routine file that passes through most corporate email filters without a second glance. However, the internal data is not a PDF at all, but an executable script designed to trigger a payload upon opening. This is the classic extension spoofing attack, a simple yet effective method where attackers rename malicious files to bypass basic filtering systems that rely on file names to determine safety.
The Architecture of Magika 1.0.2 and OpenAI Integration
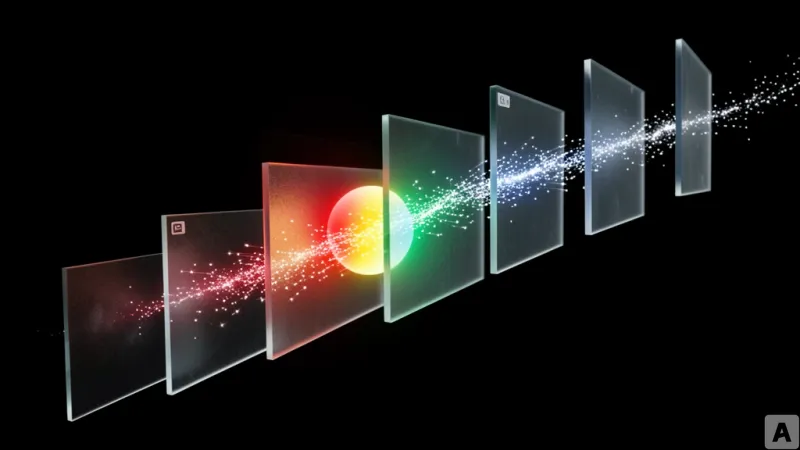
To counter this vulnerability, a new automated workflow integrates Magika 1.0.2, a deep learning-based file type detection tool, with OpenAI's large language models. Unlike traditional security tools that trust the file extension, this system ignores the filename entirely and analyzes the raw bytes of the file. By examining the binary data directly, the system can classify the actual nature of the file regardless of how it is labeled.
The operational pipeline begins with the installation of the Magika library and the establishment of a connection to the OpenAI API. Within this framework, Magika operates using specific prediction modes and confidence settings. These settings determine how the system handles ambiguous inputs, ensuring that the tool does not make a blind guess when a file's byte signature is unclear. To handle enterprise-scale data, the system employs batch scanning, allowing it to process massive volumes of files simultaneously. The output of this process is a structured JSON report, providing a standardized data exchange format that can be ingested by other security tools.
In a production security pipeline, the system compares the actual file type detected by Magika against the expected extension. This comparison triggers a logic gate that decides whether to allow the file, flag it for review, or block it entirely. For deeper forensic analysis, the pipeline generates indicators of compromise by inspecting SHA-256 hash prefixes and MIME types. This ensures that every file has a unique digital fingerprint and a standardized internet media type associated with it.
Beyond individual files, the system analyzes entire data repositories where code and configuration files are often intermingled. By grouping files based on the labels provided by Magika, the pipeline feeds the distribution data into GPT. The model then analyzes the overall composition of the repository to determine its purpose and identify potential maintenance concerns or security gaps. The underlying model achieves this by analyzing only a small portion of the leading bytes of a file, providing a confidence score alongside its identification.
From Byte Detection to Business Risk Interpretation
Traditional file analysis has long relied on static signature matching or simple extension-based classification. This approach creates a structural weakness because the detection mechanism is decoupled from the actual content. If an attacker changes a .exe to a .jpg, the system sees a picture. Magika fundamentally shifts this dynamic by moving the point of detection to the byte level, where the identity of the file is immutable regardless of its name.
The real breakthrough, however, is not the detection itself but the interpretation of that data. A standard security tool might report a MIME type mismatch, a technical observation that requires a human analyst to interpret. This pipeline takes that technical mismatch and passes it to OpenAI, which transforms the raw data into a concrete security insight. Instead of a log entry stating a type mismatch, the system generates a report explaining that an attacker is attempting to distribute malicious code disguised as a PDF.
This transition represents a significant leap in the operational efficiency of a Security Operations Center (SOC). It creates a direct path from low-level byte detection to high-level executive reporting. By automating the translation of technical facts into business risks, the system removes the need for manual intervention by an analyst to explain the threat to stakeholders. The value of file analysis has moved from simple classification to contextual understanding.
Integrating the translation of technical indicators into language that non-expert decision-makers can understand allows for faster response times. The pipeline ensures that the technical reality of a threat is immediately visible as a business liability.
Security is no longer a battle of what can be found, but how quickly the findings can be interpreted to drive a decision.